MTG Corporate Public Key Infrastructure
Our PKI Architecture at a Glance
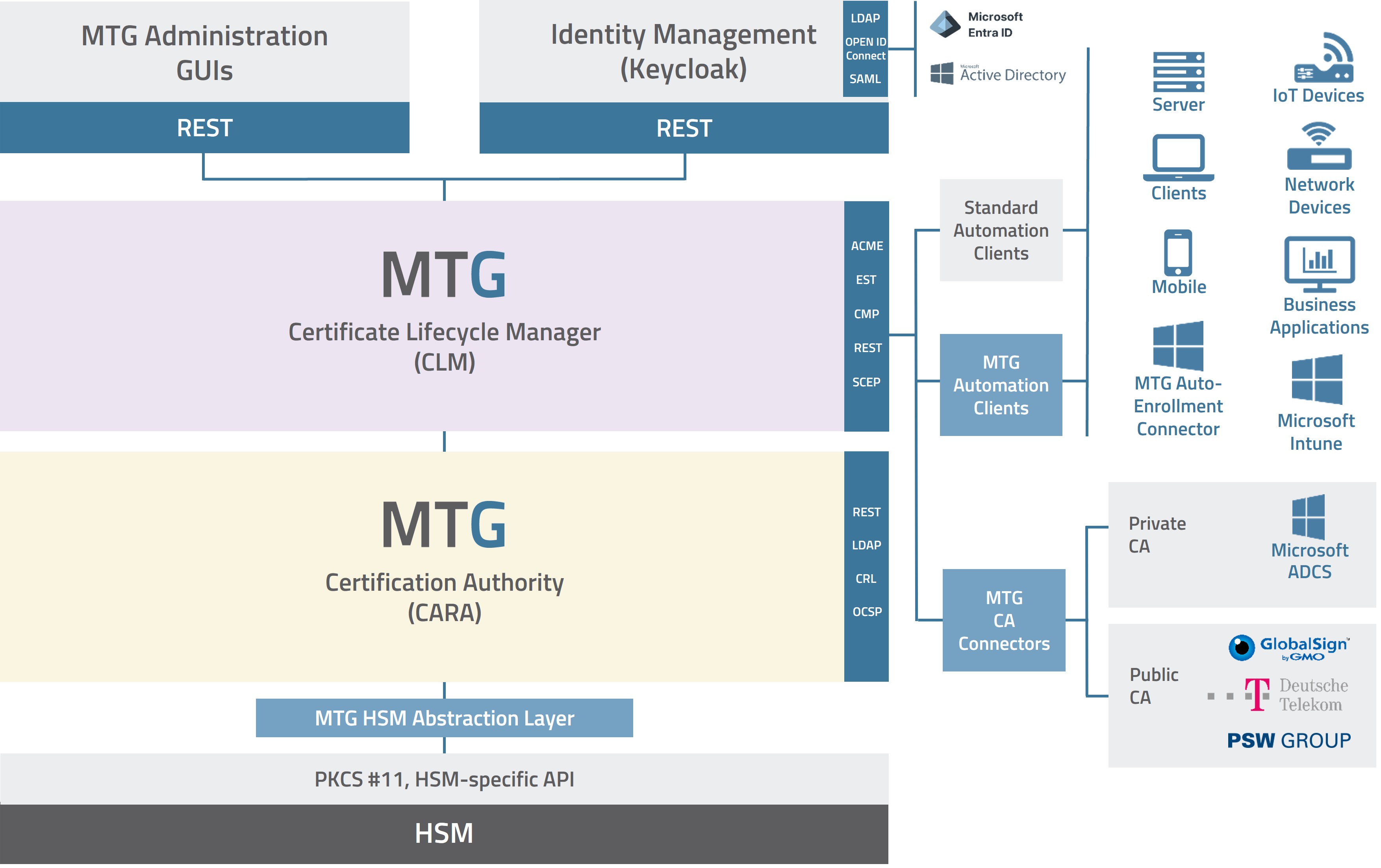
MTG Corporate PKI Architecture (© MTG AG)
MTG Corporate PKI consists of two aligned product components of the MTG ERS ® System: MTG Certificate Lifecycle Manager and MTG Certificate Authority (MTG CARA), and thus offers protection for many use cases in companies.
MTG Certificate Lifecycle Manager

CLM Dashboard (© MTG AG)
The MTG Certificate Lifecycle Manager (CLM) ensures the smooth and automated management of all certificate-based processes. It improves process quality and reduces costly downtime caused by inadvertently expired certificates. In addition, the system provides a complete overview of the status and deployment locations of all certificates. Compliance policies can be implemented flexibly and are supported by detailed role- and permission-based settings.
Insight into the MTG CLM Dashboard
In this video, you'll get a compact overview of the MTG CLM Dashboard. See how you can effortlessly manage, monitor, and renew certificates, all on a user-friendly and intuitive platform.
Key Features of MTG CLM at a Glance
- Automation
With widely used automation protocols such as ACME, EST, CMP, and SCEP, as well as a powerful REST API, you can significantly reduce manual effort and minimize potential errors in certificate management. - Multiple Business Domains
Structure your PKI into individual business domains. This allows you to clearly separate tenants, departments, or application areas and organize certificate management flexibly according to your requirements.. - Monitoring & Reporting
Maintain full visibility into certificate lifetimes, status, and usage at all times. Transparent reports support compliance, audits, and risk mitigation. - Notification Features
Automated notifications alert you in advance about expiring certificates or required actions, helping you avoid outages and unplanned service interruptions. - Certificate Policies
Define and standardize certificate policies using centralized templates, reducing the risk of errors and misuse during certificate requests. Requirements such as validity periods, key lengths, or intended usage can be enforced consistently. - Role and Permission Management
Configure fine-grained roles and permissions to clearly separate responsibilities and enhance security. This can be extended to allow users self-service capabilities for managing their own certificates. - Microsoft CA Connector
Seamlessly connect existing Microsoft PKI environments to our CLM and request as well as manage these certificates through our certificate lifecycle management platform. - Autoenrollment Connector
With the Autoenrollment Connector, you can migrate your existing Microsoft PKI (AD CS) to the MTG PKI (Certificate Authority) without changing established Active Directory processes. Autoenrollment, Group Policies, and Windows certificate processes remain unchanged, while certificate issuance is transitioned to the MTG CA. - Public CA Connector
Integrate public certificate authorities easily and manage external certificates centrally through a single platform. Currently supported providers include GlobalSign, Telekom, and selected Sectigo certificates via PSW. - Central Identity Management (Keycloak)
Leverage integrated identity management based on Keycloak. The system supports Microsoft Entra ID and Active Directory for seamless user and role integration. - Microsoft Intune Support
Integrate CLM into your Intune environment and centrally manage certificate deployment for mobile devices. - HSM-Support
Protect sensitive cryptographic keys with Hardware Security Modules (HSMs). Our solution supports a variety of vendor-independent HSM solutions to ensure maximum security for cryptographic keys and operations.
FREE Managed PKI & CLM – Start at no cost
MTG Certification Authority
MTG CARA is a flexible PKI platform for deploying certification authorities (CAs) and registration authorities (RAs) to issue, manage, distribute, and validate digital certificates. The platform supports multi-tenancy, crypto agility, post-quantum cryptography, and the integration of Hardware Security Modules (HSMs).
MTG CARA has been continuously developed since 2006 and has proven itself in numerous applications and trust center environments, supporting the high-performance issuance of millions of certificates. It meets all technical requirements needed to comply with demanding security standards such as BSI TR-03145 for PKI operations. The platform covers all essential PKI functions and is suitable for building and operating highly secure PKI and trust center infrastructures. It also meets the requirements of regulated or certification-critical environments.
Microsoft PKI Integration or Migration
Many organizations already use a Microsoft PKI and are looking for a suitable CLM solution to simplify certificate management. This can be easily achieved with MTG CLM
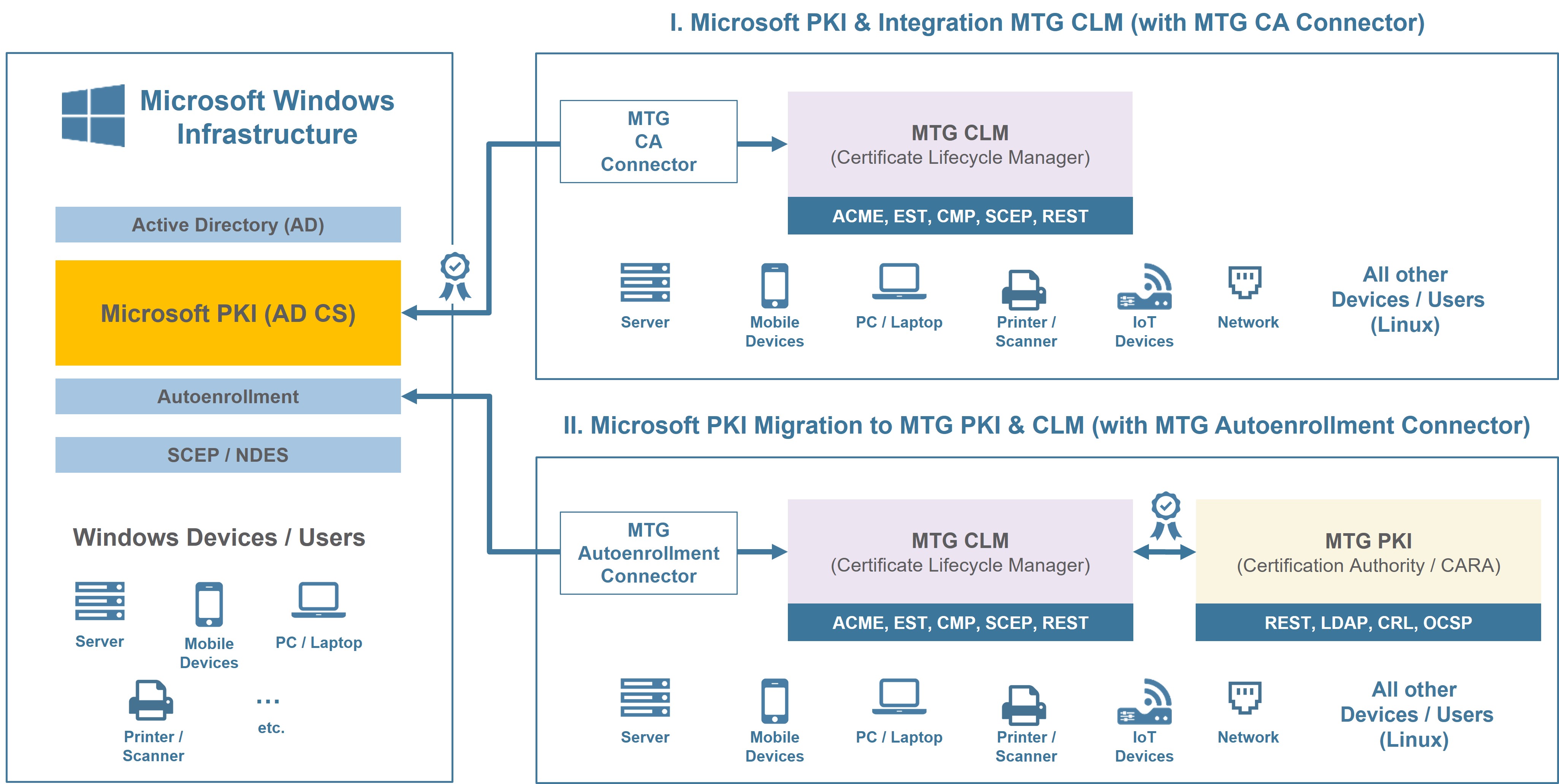
Microsoft PKI Integration and Migration (AD CS) (© MTG AG)
Scenario I: Microsoft PKI Integration with MTG CLM
Are you using Microsoft PKI (AD CS)? Then, enhance your existing PKI with MTG’s professional Certificate Lifecycle Management.
With the MTG CA Connector, you can easily integrate MTG CLM with your existing Microsoft PKI, which continues to operate as your certification authority. At the same time, you benefit from the comprehensive features and automation capabilities of the MTG Certificate Lifecycle Manager.
Scenario II: Microsoft PKI Migration
Looking to replace your Microsoft PKI? With the MTG Autoenrollment Connector, you can migrate to the MTG PKI (CARA) gradually or in full while keeping your existing Active Directory processes intact.
Autoenrollment, Group Policies, and existing Windows certificate processes continue to operate as usual, while certificate issuance is handled by the MTG CARA Certificate Authority.
PKI Use Cases: Comprehensive Implementation
The MTG Corporate PKI enables the flexible implementation of a wide range of certificate-based processes and use cases – regardless of industry, infrastructure, or security architecture.
To successfully implement certificate-based use cases, three clearly defined functional building blocks work together: (1) Certificate Creation & Lifecycle Management, (2) Certificate Distribution, and (3) Certificate Usage.
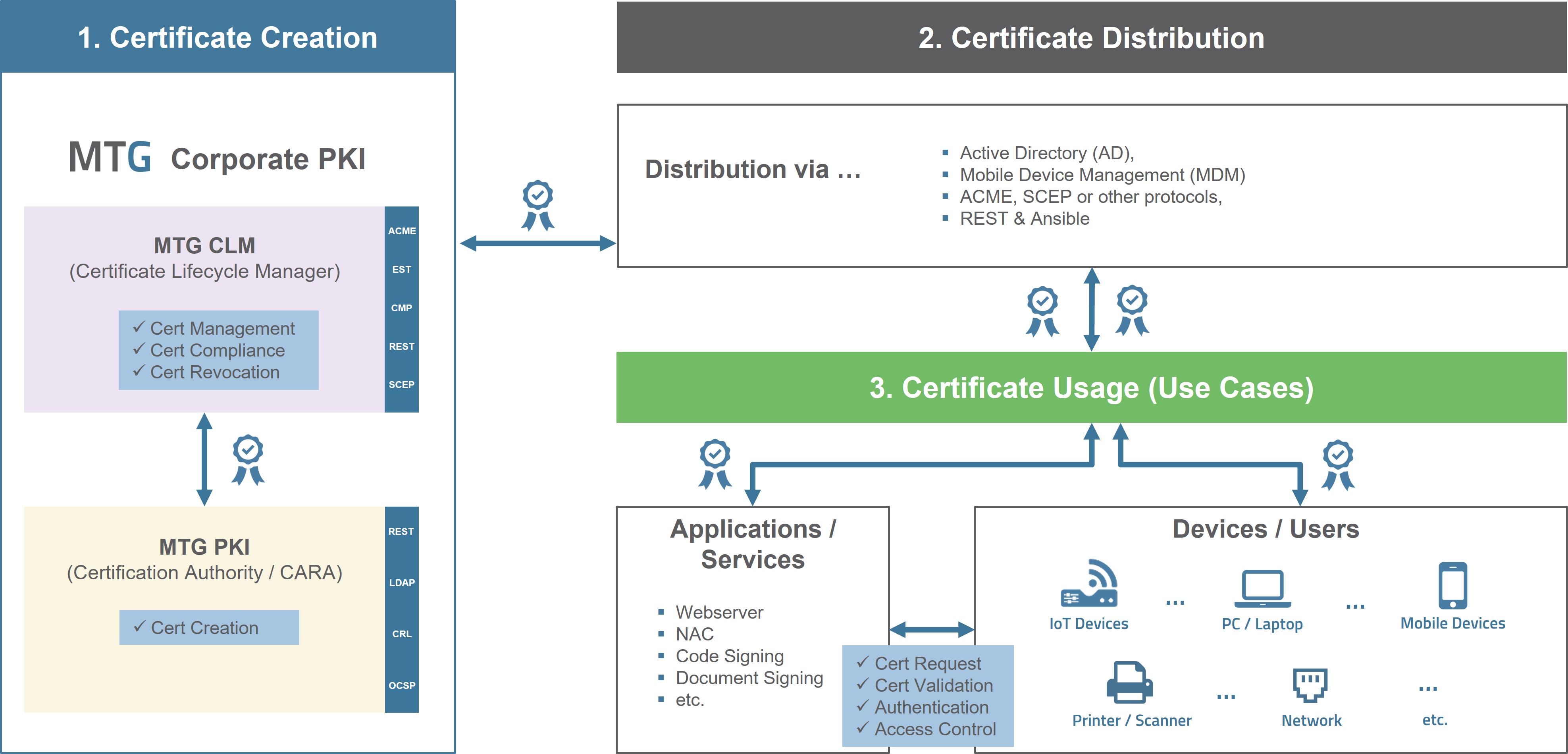
Implementation PKI Use Cases (© MTG AG)
Certificate Creation: The MTG PKI (CARA) operates the central Certification Authority and issues cryptographically secured digital certificates in accordance with defined policies. The MTG CLM manages the entire certificate lifecycle – from automated request and issuance to renewal or revocation.
Certificate Distribution & Usage: Certificates must be securely distributed to target systems such as servers, clients, or devices. This can be achieved, for example, through Active Directory, MDM solutions, automation protocols, or APIs. A prerequisite is that target systems – such as devices – and applications support certificates. In these environments, certificates enable authentication, encryption, and digital signatures.
With MTG Corporate PKI, you establish a powerful foundation for your security architecture. When designing the specific distribution and integration setup, we can support you as needed together with experienced consulting partners.
Common PKI Use Cases
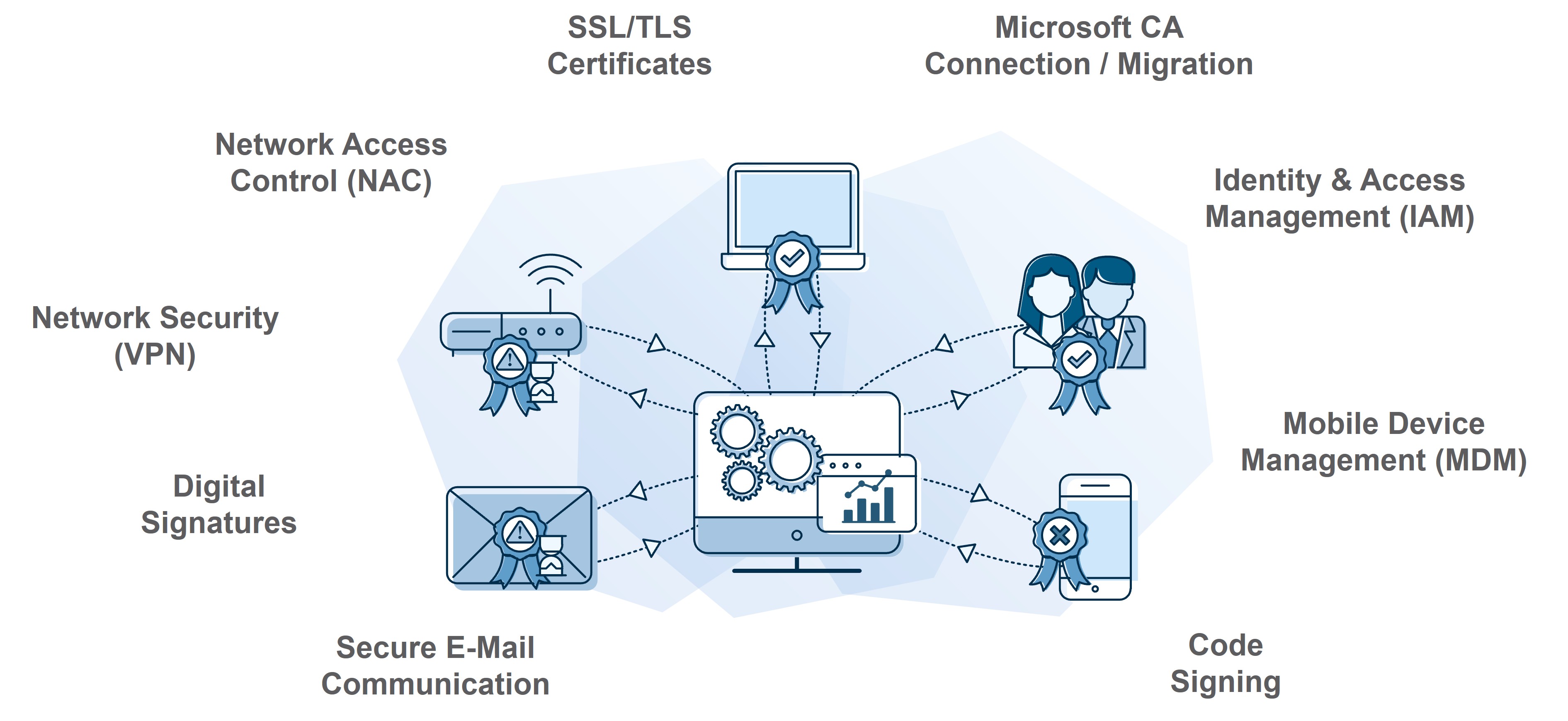
PKI Use Cases (© MTG AG)
- Identity and Access Management
Certificate-based authentication for users, systems, and services is the foundation for strong identities and controlled access models. - Network Security (VPN)
Secure remote access by uniquely identifying clients and gateways using digital certificates. - Network Access Control (NAC)
Network access restricted to authorized and trusted devices – verifiable and compliant with defined policies - Secure Email Communication
Protect sensitive content through encryption and digital signatures to ensure integrity and authenticity. - SSL/TLS Web Server Certificates
Secure internal and external applications through encrypted connections and verified server identities. - Mobile Device Management (MDM)
Certificate-based security for mobile devices to enable secure access to corporate resources. - Digital Signatures for Documents
Verifiable integrity and origin of electronic documents to support legally compliant digital business processes. - Code Signing
Trusted signing of software and updates to protect against tampering and ensure software integrity.
The right Operating Model for your PKI
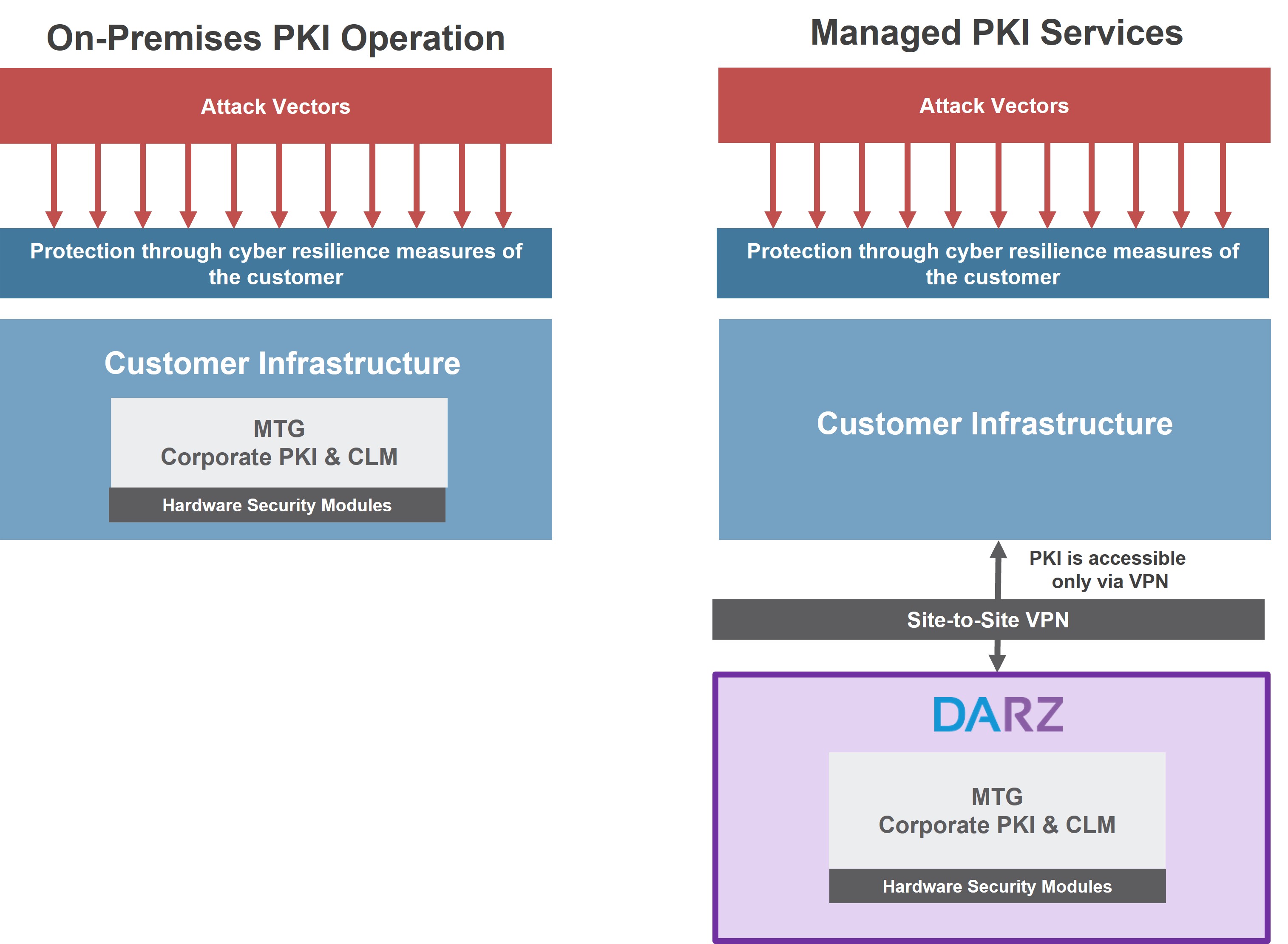
On-Premises vs. Managed PKI (© MTG AG)
The MTG Corporate PKI can be deployed On-Premises within your own infrastructure. In this model, the PKI is fully integrated into your IT and security architecture. The operation and management are handled either by the internal team or by us. Processes, key management, and compliance implementation remain under the responsibilities you define.
Alternatively, the PKI can be provided entirely as a Managed PKI Service through our partner DARZ GmbH, operated in its highly secure data centers in Darmstadt and Frankfurt. Operation takes place in a professionally secured, certified environment with clearly defined responsibilities and reliable data sovereignty. The DARZ Managed PKI & CLM can be accessed in two ways: by default, a site-to-site VPN is established. Alternatively, access can be provided over the public internet, restricted to specific IP addresses.
We are happy to support you in choosing the right operating model and ensuring an efficient implementation of your PKI project – whether On-Premises or as a Managed Service.
Choosing the right operating model depends on your regulatory requirements, available resources, and the level of protection required for your data and key material. Key factors include standards such as BSI TR-03145, industry-specific security requirements, and any necessary certifications. It is also important to consider whether you have the required PKI and security expertise available internally. Ultimately, you need to decide whether you want to take responsibility for operating the PKI and obtaining the necessary certifications yourself, or opt for a professionally managed service such as the DARZ Managed PKI & CLM.
Downloads & Links
German Article on egovernment.de
Guide to Implementing a Public Key Infrastructure Solution (de)
German Article on chemietechnik.de
End-to-end encryption secures production and development (de)
German Article on automation-next.com
PKI in Industry: Security Against Cyberattacks (de)
German Article on industrieanzeiger.industrie.de
The Importance of Encryption for the Industry of the Future (de)




