MTG IoT PKI
Provisioning of Initial Certificates in Production
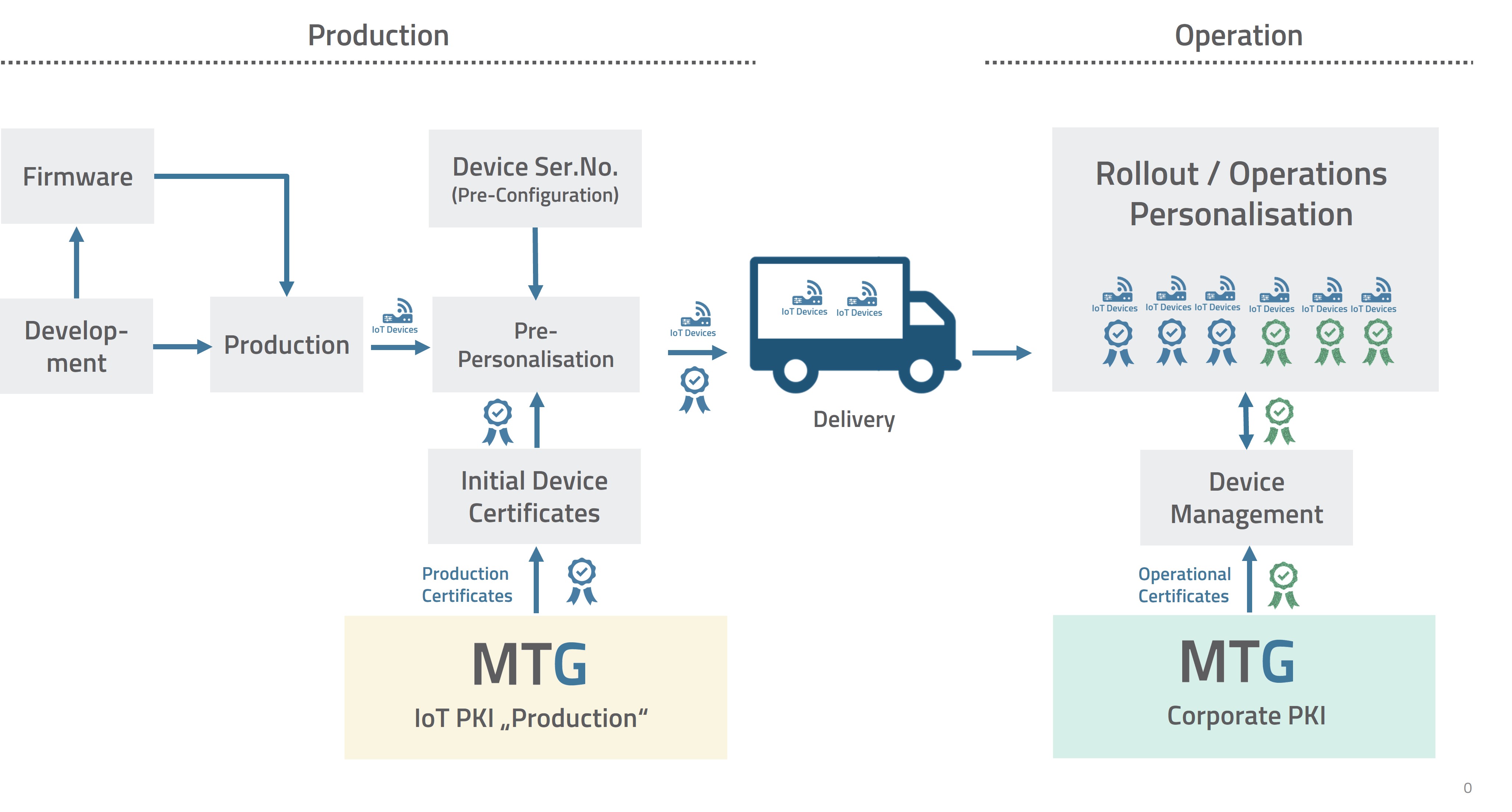
Provisioning process for IoT devices (© MTG AG)
Generation of Device Identities during the Manufacturing Process
During development and manufacturing, devices receive their firmware and operating parameters. Serial numbers and manufacturer identifiers are assigned. In the pre-personalization phase, each device receives its unique identity by requesting a certificate from the MTG IoT PKI.
The device generates its secure, unique key pair. A certificate signing request is then created and transmitted to the MTG IoT PKI “Production“.
After validation, the IoT PKI issues the corresponding initial device certificate, which is installed directly on the device. As a result, every device can be uniquely identified and authenticated with its certificate even before leaving the factory.
The entire process is fully automatable and scalable and designed to support very high production volumes with short cycle times.
Lifecycle of Device Certificates
Device certificates have defined validity periods. These must align with the planned operational lifetime of the device and the applicable security requirements. Best practice recommends certificate lifetimes of two to seven years.mBefore operational use, the device certificates must be replaced within this period by new certificates from the organization’s own corporate PKI. This takes place via device management, which requests and issues new certificates from the corporate PKI through standardized interfaces such as EST or CMP. Device management ensures that these certificates are renewed in time before their respective validity period expires. Without renewal, the devices lose their communication capability after the certificate validity period expires and therefore their functionality. Usually, they can then only be replaced or brought back into operation with considerable effort.
Independent PKI Architecture for Production and Operation
The MTG IoT PKI for production and the MTG Corporate PKI for operation work independently of each other. The replacement of the production certificates during operational use is manufacturer-independent and can be carried out with any suitable corporate PKI.
In times of increasing cyberattacks and regulatory requirements such as the NIS2 Directive and the Cyber Resilience Act (CRA), a reliable PKI is essential for securing device identities.
Overview: Features of the MTG IoT PKI
- Automated Certificate Provisioning in Manufacturing
Certificates are generated and installed directly in the production process. Integrable into existing production lines and calibration processes. Suitable for high quantities and short cycle times. - Manufacturer-Specific Licensing Model
Licensing of the MTG IoT PKI is based exclusively on the number of certificates issued in the calendar year. The decisive factor is your actual annual production. License costs for already issued active certificates do not accumulate over several years. This is particularly relevant when certificates must continue to be maintained in revocation lists at the customer’s request. - Unique Device Identity from the Factory
Each device receives a cryptographically secured, unique identity. Protection against counterfeiting, replacement of components, and manipulation already before delivery. - Secure Key Generation in the Device
Private keys are generated directly in the device. Alternatively via secured production clients. No export of sensitive key material. - Integration into Existing Production Processes
Support for pre-personalization, firmware flashing, calibration, and assignment of serial numbers. Seamless integration into manufacturing and test environments. - Scalable for Series and Mass Production
Designed for industrial quantities. Stable even with very high certificate volumes per day. - Defined Validity Periods for Production Certificates
Flexible definition of individual certificate validity periods for the initial certificates. - Manufacturer-Independent PKI Used in Operation
The replacement of the initial production certificates is manufacturer-independent and possible with suitable PKI systems. - Certificate Lifecycle Management
All certificate-based processes and automation options can be organized with the integrated Certificate Lifecycle Management. This includes, for example, the setup of areas for different production sites with finely granular rights and role assignments.
PKI for Industrial Communication Networks and Machine Control Systems
With certificates from the MTG Corporate PKI, industrial communication networks, machine control systems, and connected production environments can be reliably secured. Against the background of regulatory requirements such as NIS2, the Cyber Resilience Act, or IEC 62443, it supports the technical implementation of security requirements for authentication, integrity, and encrypted communication and creates the basis for compliance and auditable security structures.
Industrial communication standards such as OPC UA can also be fully integrated with the MTG Corporate PKI and use certificate-based authentication and encrypted communication in accordance with industrial security requirements.
Certificates enable strong authentication, protected machine communication, and digitally signed software updates. In this way, rollout, remote maintenance, global production control, and maintenance processes are implemented securely and efficiently.
The architecture also supports hybrid encryption methods and post-quantum cryptography in order to protect industrial systems against future threats in the long term.
MTG IoT KMS – Optimal Complement to the IoT PKI for Comprehensive Device Security
In modern device production, the trend is increasingly toward the combined use of Public Key Infrastructure (PKI) and a Key Management System (KMS). The PKI provides identities and certificates. The KMS handles the secure generation, storage, management, and use of cryptographic key material.
With the MTG IoT KMS, MTG offers the appropriate complement to the MTG IoT PKI. Both solutions interact seamlessly and enable a consistent security architecture for keys and certificates.
This holistic approach is the central idea of the MTG ERS® architecture. It ensures that identities and keys are managed in a consistent, secure, and scalable way throughout their entire lifecycle.
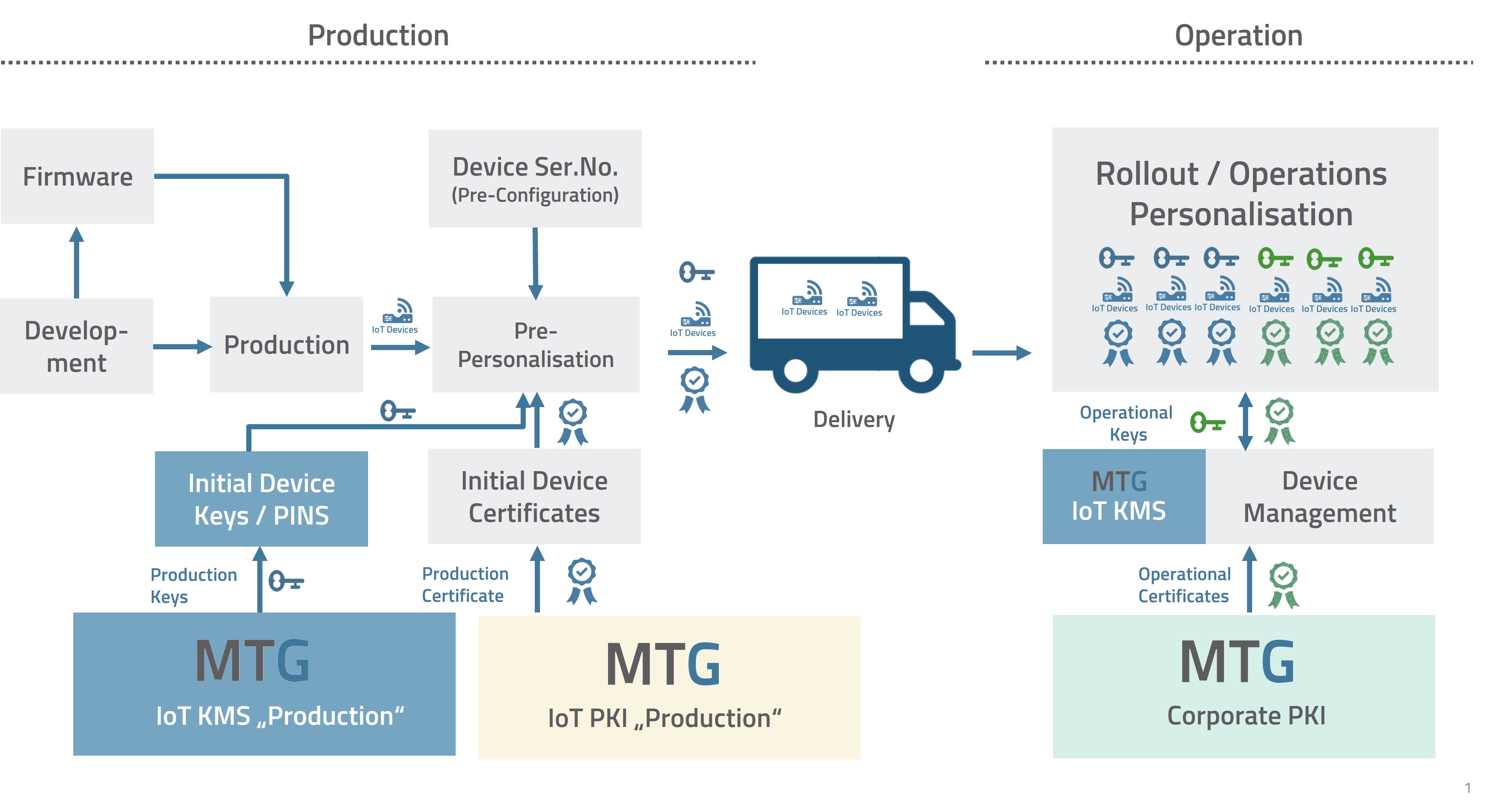
IoT PKI KMS extension (© MTG AG)


