HSM Integration
Vendor-independent HSM integration by MTG
MTG’s vendor-independent HSM integration is based on the MTG ERS® components for PKI and KMS. It can be flexibly integrated into both existing and new ERS® infrastructures.
Depending on the requirements, integration is implemented either via established standard interfaces or through a specially developed MTG HSM abstraction layer. This enables HSMs to be flexibly integrated into higher-level security and lifecycle processes. The MTG HSM abstraction layer reduces dependency on individual vendors, simplifies migrations, and facilitates integration into complex IT environments.
Among others, HSM solutions from Securosys, Utimaco, Entrust, and Thales are supported. This allows companies to maintain their existing vendor strategies, implement multi-vendor scenarios, and future-proof the further development of their HSM landscape.
MTG is a technology partner for HSM solutions from Utimaco and Securosys.
HSM Consulting
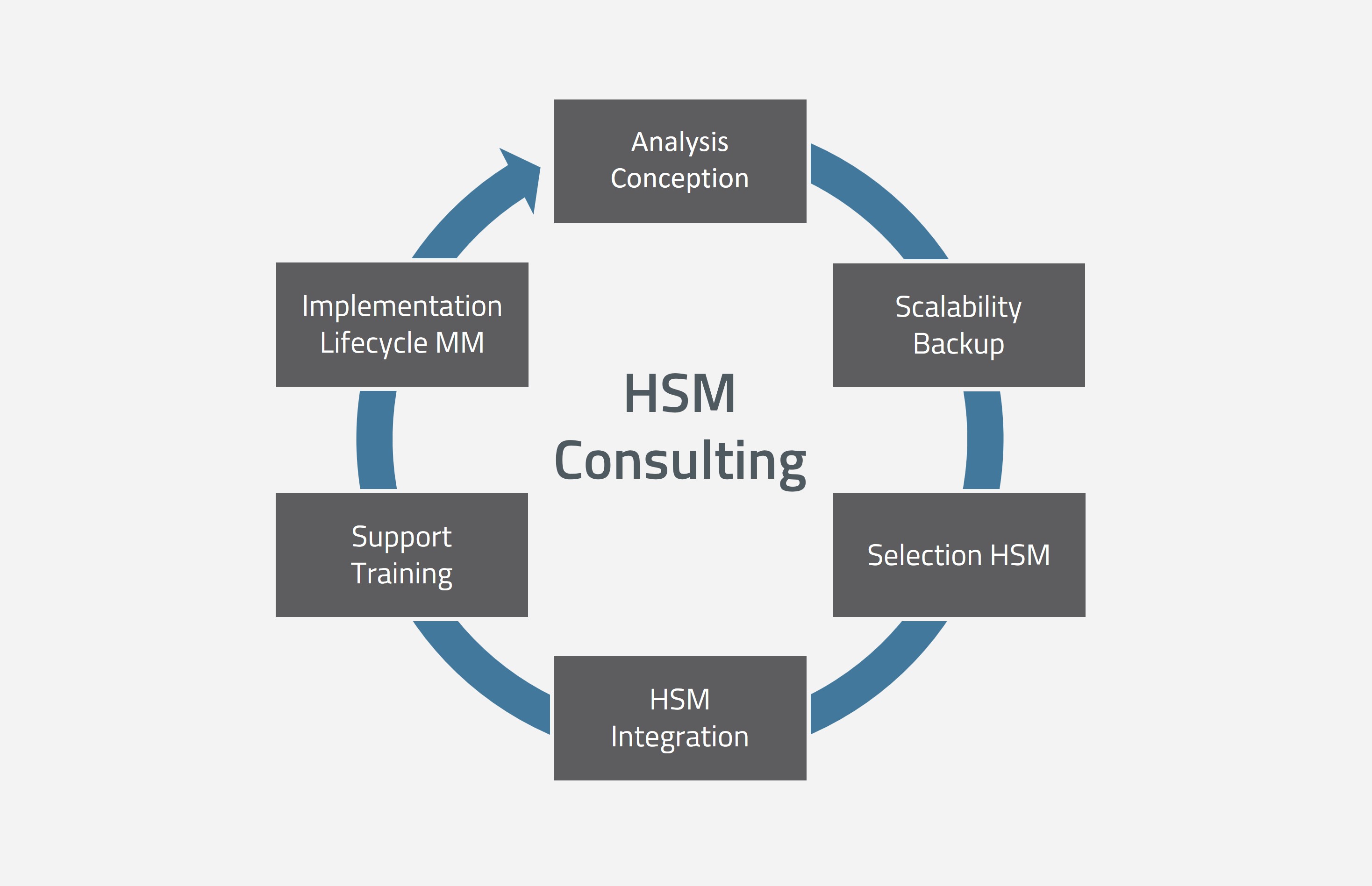
MTG HSM Consulting (© MTG AG)
MTG Services
- Analysis, design, and specification of requirements
- Definition of scalability, high availability, and backup strategies
- Selection of suitable HSM models
- Integration of HSMs into existing or new ERS® infrastructures
- Ongoing support, training, and operational assistance
- Consulting on the implementation of security lifecycle management, for example on role and authorization concepts as well as the four-eyes principle


