New Security Requirements for Building Automation
Cybersecurity is increasingly becoming a fundamental requirement for the planning, operation, and devices used in building automation. The NIS2 Directive and the BSIG mandate operators of critical infrastructures to implement adequate risk management and effective security measures. At the same time, the Cyber Resilience Act (CRA) raises the requirements for manufacturers of devices and components.
For building automation, this means that communication must be protected, device identities must be reliably secured, and trust relationships must be established in a technically sound manner. Digital certificates from a Public Key Infrastructure (PKI) play a central role in this. A PKI issues and manages these certificates throughout their entire lifecycle. They enable secure communication and form the foundation for a robust trust chain between systems and devices.
Secure Management of Device Certificates Throughout Their Lifecycle
Digital certificates are not a one-time issue. To meet regulatory requirements and ensure a high level of security, they must be managed throughout the entire lifecycle of a device. Manufacturers typically equip their devices with initial certificates during production. However, before operational use in the building, these certificates must be replaced with certificates from a trusted corporate PKI of the building management. Additionally, certificates expire and must be monitored, renewed in time, and properly replaced.
With BACnet Secure Connect (BACnet/SC), building automation has created the necessary conditions to respond to increased security requirements. BACnet/SC-enabled devices use digital certificates to secure communication and establish trusted device identities.
Making BACnet/SC Practically Automatable for the First Time
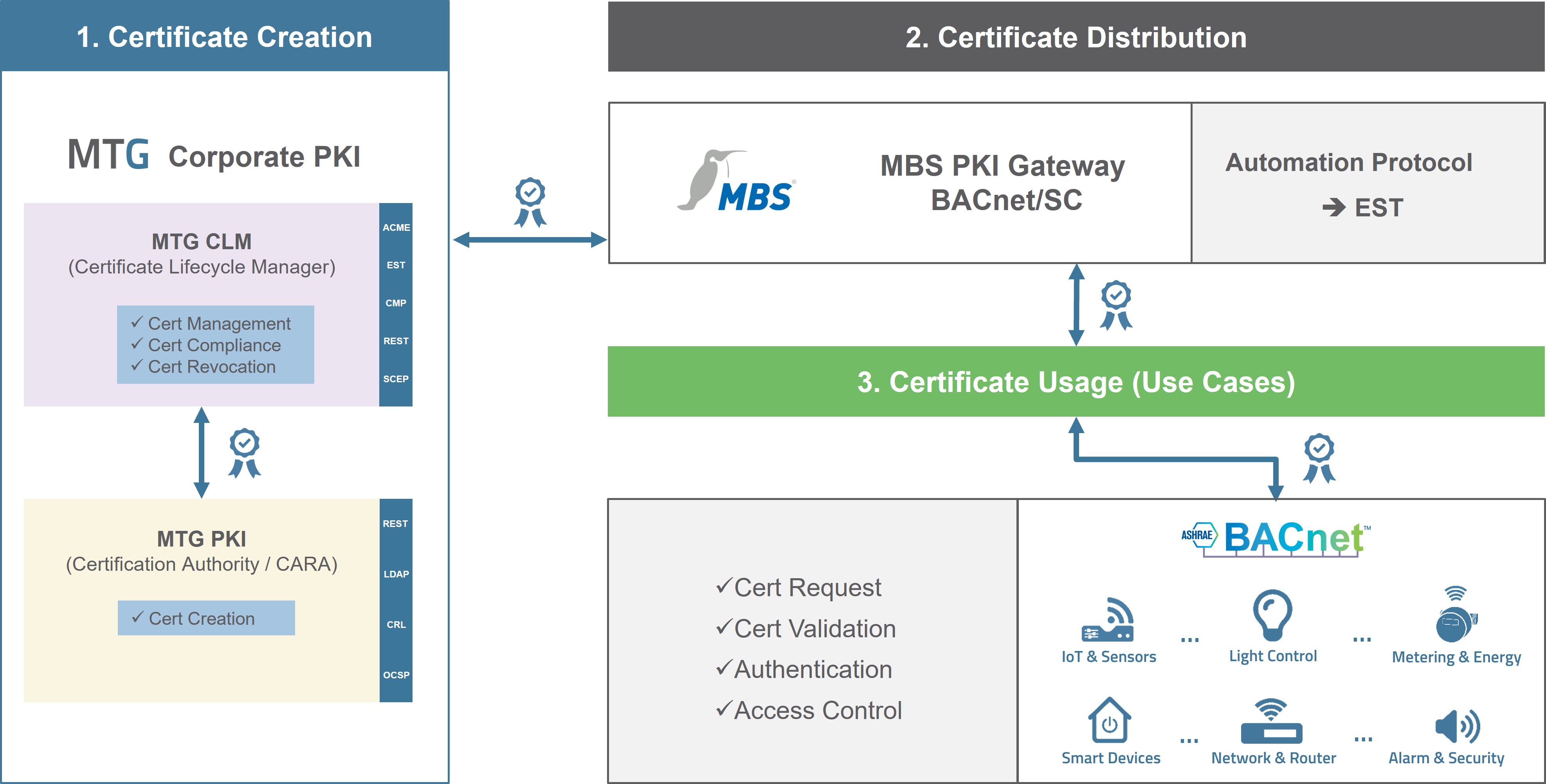
Figure (© MTG AG)
After delivery, manufacturer certificates typically need to be replaced with certificates from building management – a process that, in practice, has mostly been done manually for each device. For a few components, this may still be manageable. However, in larger buildings with many interconnected devices, different manufacturers, and varying certificate lifetimes, this approach results in significant effort and, consequently, higher costs.
Unintentionally expired certificates can, as a result, cause building automation to fail either partially or entirely. Manual processes are prone to errors, operational costs increase, and certificate lifetimes must be constantly monitored. This significantly limits the practicality for real-world buildings. Additionally, the economic implementation of new security requirements becomes more challenging.
In practice, a central challenge arises: Manual management of certificates does not scale.
The real challenge lies not in the lifespan of individual certificates, but in the efficient and scalable management throughout their entire lifecycle.
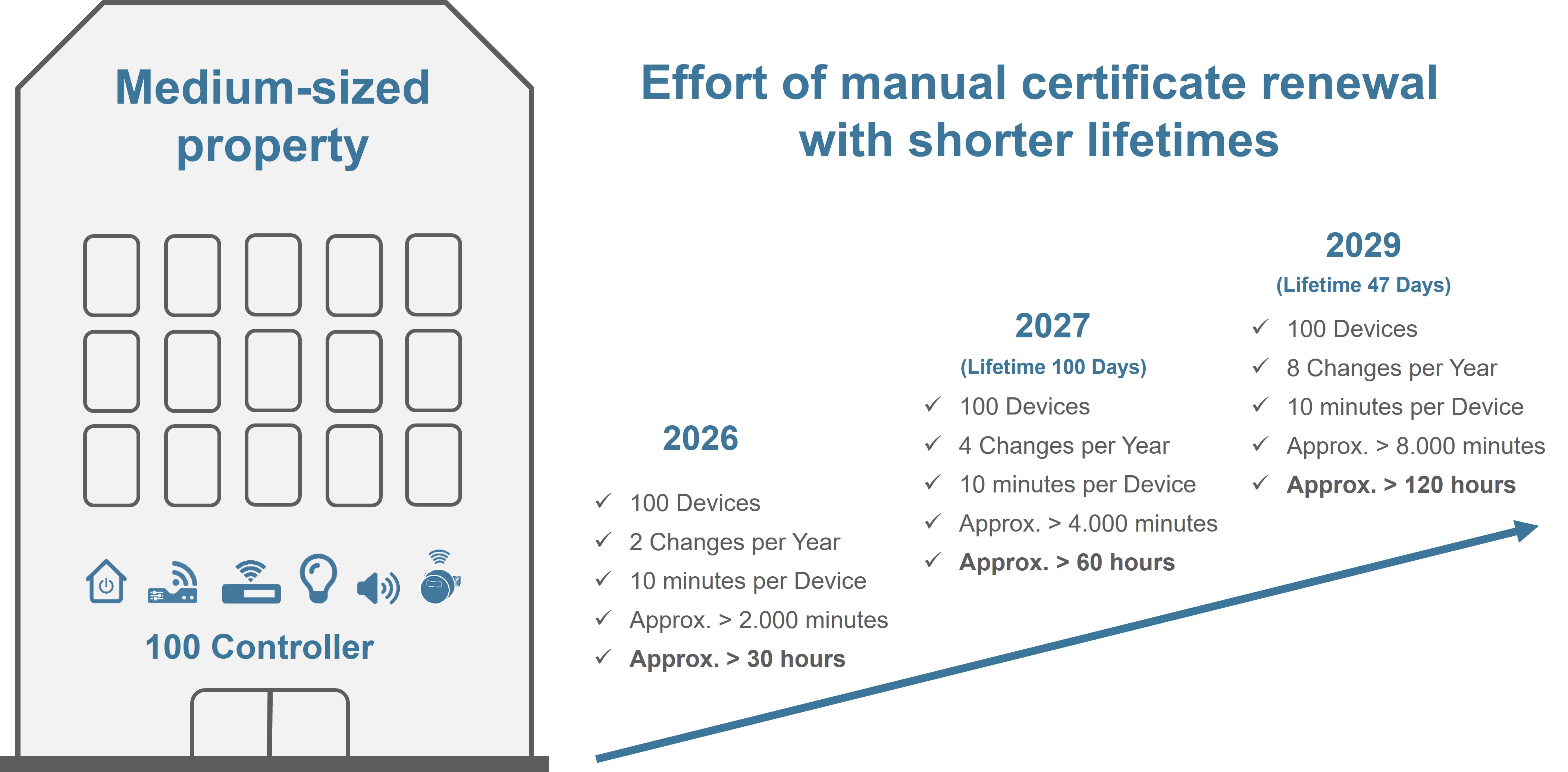
Calculation example for the manual effort of certificate renewal in a medium-sized property (© MTG AG)
A simple Example Illustrates the Effort
If the setup or replacement of a certificate per device is estimated to take only 10 minutes – which is quite an optimistic value – for 100 controllers in a medium-sized property, the effort already amounts to 1,000 minutes per cycle.
With two required certificate renewals per year, this equals approximately 2,000 minutes or over 30 hours annually. At the same time, there is a clear trend in the IT world towards significantly shorter certificate lifetimes. Decisions from the CA/Browser Forum foresee lifetimes of well under 100 days in the future, with only 47 days allowed starting in 2029. For the same property, this would mean: The manual effort increases from around 30 hours to well over 120 hours annually. This would reach a scale that is hardly manageable manually.
Although these requirements are not directly transferable to building automation, they point in the right direction: Shorter lifetimes reduce the risk of compromised keys and sustainably increase the security of systems. In practice, lifetimes of six to twelve months are often chosen – as a conscious compromise between security requirements and operational effort. However, with an increasing number of interconnected devices and rising IT security requirements, it becomes evident: Manual processes quickly reach their limits.
In practice, additional complexity arises, as devices replaced mid-year and staggered processing windows often lead to different certificate lifetimes. This makes transparency, control, and the automated renewal of certificates even more important in order to reduce the risk of accidentally expired certificates and misconfigurations.
With an appropriate PKI, the automation of certificate requests and certificate renewals is generally possible. Standard protocols such as EST, CMP, or SCEP provide the foundation for this. While BACnet/SC allows secure communication with certificates, it does not directly support the automation of certificate processes via standard protocols like EST or CMP, which are typically used for devices.
The deployed PKI can also become a limiting factor if it does not support these automation protocols. A widely used Microsoft PKI can issue certificates, but without support for protocols like EST, continuous automation is not possible.
The Solution: The MBS PKI Gateway | BACnet/SC supports EST
This is where the PKI Gateway | BACnet/SC comes into play, implemented based on MBS Universal Gateways. MBS creates the necessary bridge between BACnet/SC and modern PKI automation. The gateway supports the EST protocol, thus providing the foundation for manufacturer-independent and automated certificate communication. MBS takes on the role of enabling communication between systems that would otherwise require significant manual effort for integration.
In combination with the MTG Corporate PKI, this approach paves the way for an efficient, automated certificate management process. Devices can be efficiently equipped with user certificates, certificates can be centrally managed, and timely renewals can be ensured. This combined approach turns a regulatory and technical requirement into a practical, usable process.
The MTG Corporate PKI can be operated locally in the building, respecting the strict requirements for zone separation. The MTG software is delivered in a specially developed virtual appliance format, making it quickly deployable with minimal setup effort. External access is strictly controlled and occurs only in secured areas. This approach offers advantages, especially in sensitive environments. Core security functions remain locally available, integration paths are clearly controllable, and the PKI can be more easily integrated into existing operational and security concepts.
Early Testing of Automated Certificate Management on Real Devices
The M&P Group has specifically expanded its proven testing setup with these innovative components from MBS and MTG. It demonstrates the current state of the art with market-standard BACnet/SC-enabled components. Set up directly at the customer's site, it represents a complete building automation system in a deliberately challenging best-case scenario, including PKI and Certificate Lifecycle Management.

M&P Group Testing Setup: Proof of Concept for OT Security with MBS PKI Gateway | BACnet/SC and MTG Corporate PKI (© M&P Group)
This allows a practical demonstration of how secure, resilient, and manufacturer-independent building automation networks can be designed and operated. Individual requirements and specific scenarios can be tested risk-free before being implemented in real projects. New security requirements in building automation can thus be examined early on. At the same time, it becomes clear how cost-efficient and automated processes can be established. This creates a concrete, testable, and manageable approach for modern building automation.
If you have any questions, please contact us. We will connect you with the right contacts at M&P Group and MBS for a PoC.


