DARZ Managed PKI & CLM
PKI & Certificate Management Made Easy –
Automation included
Organizations today use an increasing number of certificates, while security and compliance requirements continue to grow. Without a structured PKI and certificate management approach, it becomes increasingly difficult to maintain visibility over certificates, their lifetimes, and associated permissions. Certificate Lifecycle Management (CLM) provides transparency and control. Certificates can be centrally managed, automatically deployed, and renewed on time. Our system supports key PKI automation protocols including SCEP, ACME, EST, and CMP. Public certificates with increasingly shorter validity periods can also be efficiently managed with an automated CLM system. As a result, administrative effort is significantly reduced, and the risk of expired certificates is minimized. Regulatory requirements such as the NIS2 Directive and the Digital Operational Resilience Act further increase the need for structured certificate management. For affected organizations, a Managed PKI provides a fast and straightforward way to reliably meet these requirements.
Easily Extend Microsoft PKI with CLM
Microsoft PKI (AD CS) is widely used but does not include built-in certificate management. MTG CLM complements this capability by extending the existing Microsoft PKI with comprehensive, modern Certificate Lifecycle Management functionality. All essential certificate management processes can be implemented quickly and easily without replacing the existing Microsoft PKI. This allows organizations to benefit from a powerful CLM solution without introducing additional requirements for their own infrastructure.
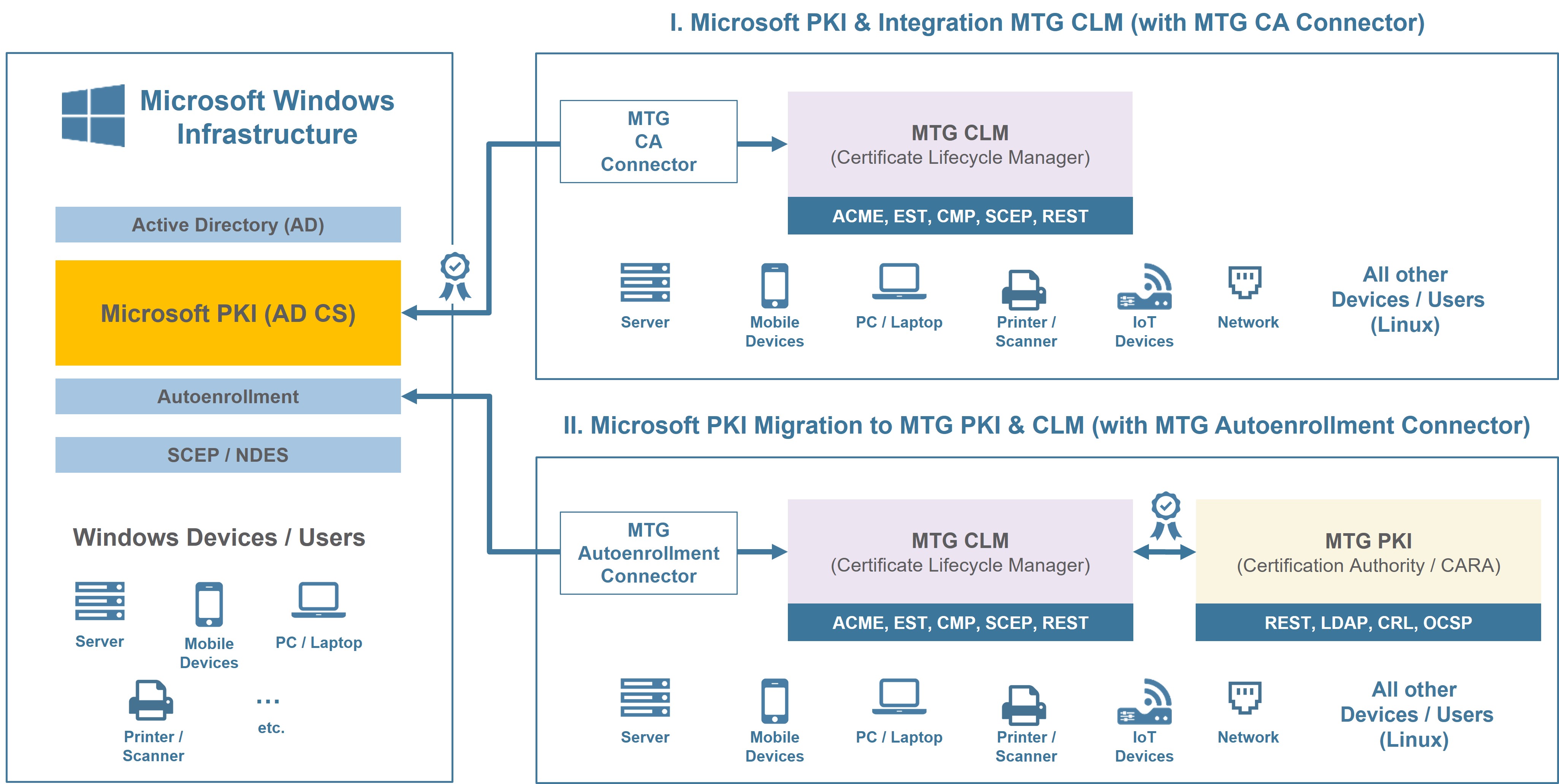
Microsoft PKI Integration & Migration (© MTG AG)
Alternatively, a migration to the MTG Certification Authority (CARA) is also possible. Thanks to the MTG Autoenrollment Connector, established Active Directory (AD) processes remain unchanged. Autoenrollment, Group Policies, and existing Windows certificate processes can continue to be used.
Fault-Tolerant Operations – Certified, Scalable, and Available 24/7
The DARZ Managed PKI & CLM is operated by DARZ and experienced IT security experts. Onboarding and secure integration with the enterprise infrastructure follow our proven standards. This allows organizations to quickly use the managed PKI service without having to invest time and resources in building their own PKI and CLM system.
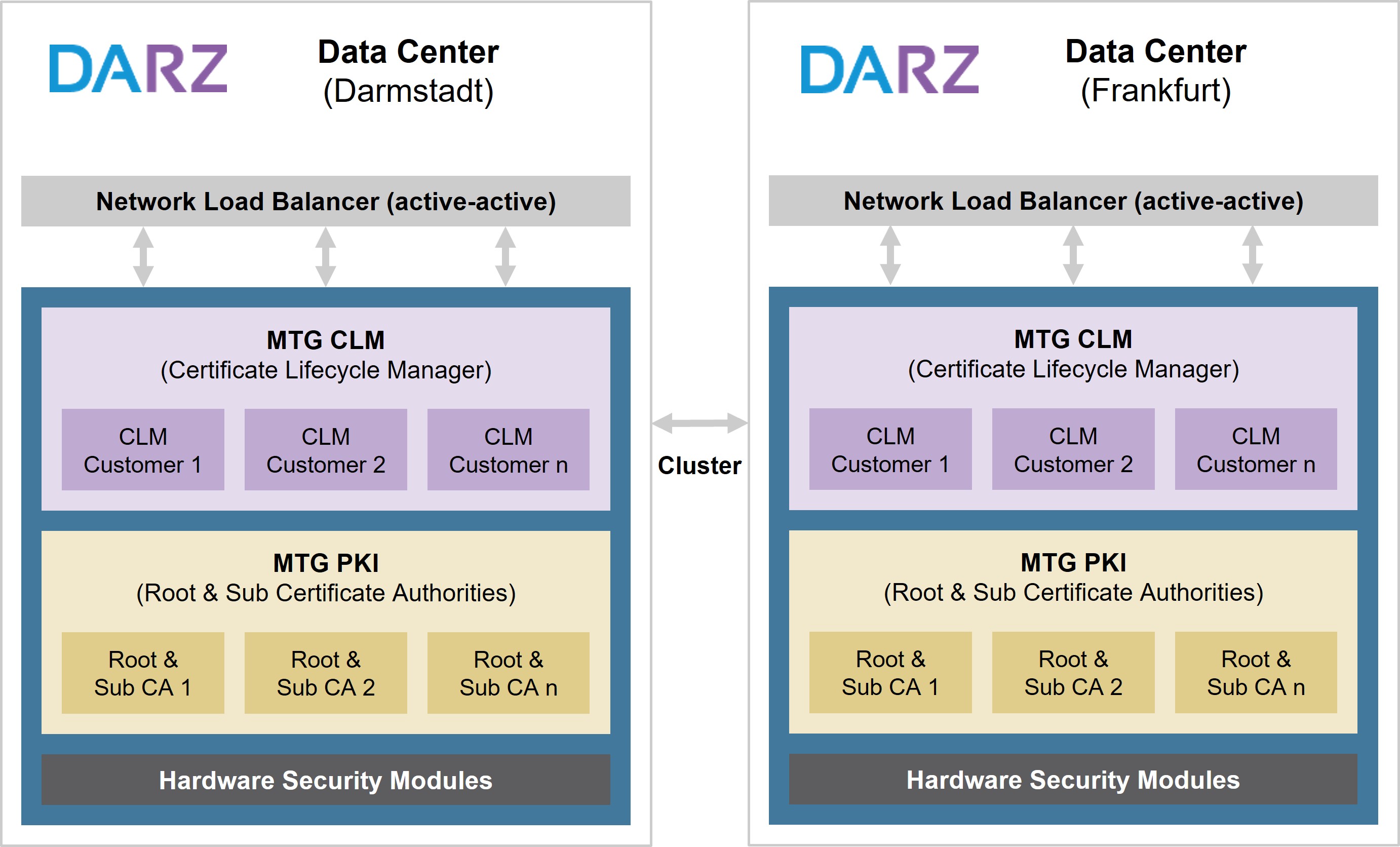
High Availability at DARZ (© MTG AG)
For each organization, a dedicated Root CA is established as the central trust anchor. Multiple Sub-CAs can operate beneath it to issue certificates for different applications, services, and systems.
The Managed PKI is operated in a highly available and scalable setup at the German locations Darmstadt and Frankfurt am Main. The signing keys of the MTG CA are protected within certified Hardware Security Modules (HSMs) compliant with FIPS 140-2 Level 3 and Common Criteria EAL4+ (EN 419 221-5).
DARZ holds all relevant certifications required for the secure operation of a PKI infrastructure.
Secure Connectivity via VPN Instead of Public Cloud
DARZ Managed PKI & CLM can be connected in two ways. By default, access is established via a site-to-site VPN connection.
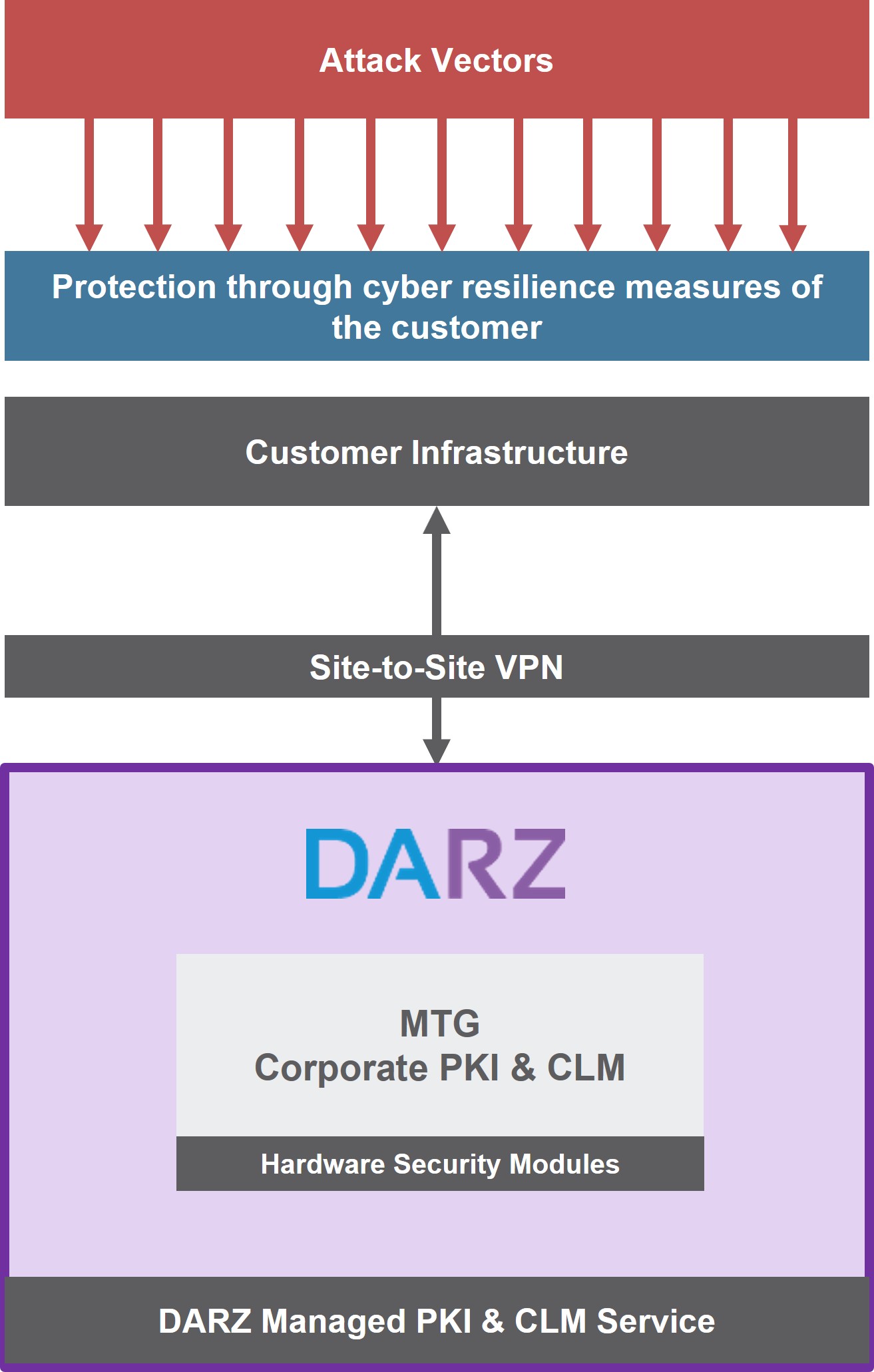
VPN - Managed PKI Services (© MTG AG)
Alternatively, connectivity can be provided via the public internet, with access restricted to defined IP addresses. This allows the PKI infrastructure to be securely integrated into existing corporate networks without requiring a public cloud connection.
Fast Access to PKI Expertise when it comes to Implementation
Organizations use a PKI to secure applications, systems, and processes with trusted digital identities. Once the PKI and CLM are connected, the next step is to implement specific use cases – for example, for devices, services, users, or machine-to-machine communication (M2M). Depending on the project and level of integration, additional expertise may be helpful. In addition to the managed service, organizations can access experienced PKI experts whenever needed.
Benefit from our many years of experience in implementing PKI-based infrastructures and processes. We understand the typical challenges – and, above all, the right solutions.
Through our partner network of PKI consultants, technology partners, and resellers, we can connect you with the right experts for your specific PKI project when needed.
Start for Free – Manage Up to 50 Active Certificates
With our FREE Plan, you can use all essential features of the Managed PKI & CLM, gain initial hands-on experience, and lay the foundation for the next step. The plan is free of charge and allows productive use with up to 50 active certificates, enabling you to take advantage of the full feature set, including automation.
Active certificates can originate from the following CAs:
- MTG CARA
- Microsoft PKI (AD CS)
- Ausgewählte Public CA Anbieter (GlobalSign, PSW/Sectigo, Telekom)
The integrated Certificate Discovery tool also allows you to scan for existing certificates across your organization and import them without limits. This makes it possible to identify certificates that may previously have gone unnoticed on servers and systems and renew or replace them in time.
In the intuitive Dashboard, you can conveniently keep track of all certificate lifetimes at a glance.
Register for your FREE PKI instance in just a few minutes
In this video, we will show you how to register for our FREE plan in under 5 minutes. Your personal, FREE PKI instance will be provisioned within 1-2 business days after a brief review.
PKI Technology Made in Germany
The technology foundation of this managed service offering is the MTG Corporate PKI & CLM.

CLM Policies Overview (© MTG AG)




